-
EternalBlue explained: What it is and how to stay safe
You may have heard of WannaCry and NotPetya, two ransomware outbreaks that caused widespread disruption around the world. What these attacks share in common is the use of an exploit called EternalBlue...
-
How to protect your phone from juice jacking attacks
It’s inevitable: phones need regular recharging, and sometimes that means topping up in public. Security researchers have shown that it's theoretically possible to compromise a phone through a proce...
-
What is a smurf attack and why is it a security risk?
A smurf attack is a denial-of-service (DoS) attack that can make systems or services unavailable without breaking into them or exploiting software flaws. Instead of targeting user accounts or applicat...
-
How to prevent a ping flood attack on your network
Not all network disruptions come from advanced malware or sophisticated hacking tools. Sometimes, everyday network behavior is simply pushed too far. A ping flood attack takes a basic connectivity che...
-
What is AI phishing, and how can you avoid it?
Artificial intelligence (AI) has become a part of everyday life for many people. It can assist with everything from meal planning to managing schedules and emails and can enhance the cybersecurity too...
-
What scambaiting is and how it works
Scambaiting is the practice of deliberately engaging with scammers, often with the goal of wasting their time or exposing their tactics. Even if it feels harmless, interacting with scammers can expose...
-
The ultimate guide to phishing detection
One of the most common types of cybercrime, phishing uses deceptive methods to trick people into sharing sensitive information, sending money, or downloading malicious software. It often relies on cre...
-

DNS over QUIC (DoQ): Everything you need to know about the new DNS protocol
Almost everything you do online starts with looking something up using the Domain Name System (DNS). Often called the internet’s address book, DNS is how your device turns a website name, like www.e...
-
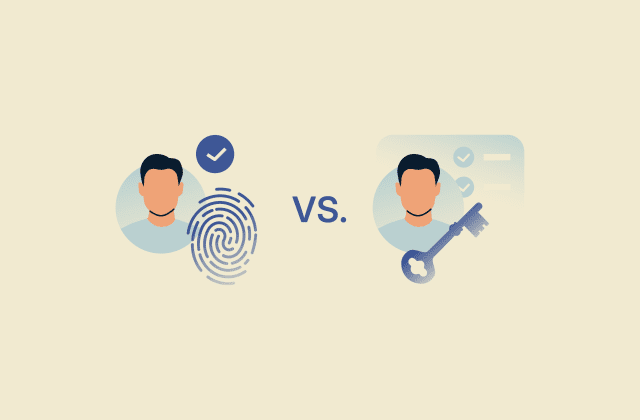
Authentication vs. authorization: What’s the difference?
Authentication and authorization are often confused, but they play distinct roles in access control and security. Together, they help control who can enter a system and what actions they can take once...
-
Phishing-as-a-Service (PhaaS): What it is and why it’s dangerous
Phishing used to require technical skills, infrastructure, and time. An attacker had to write their own emails, build fake websites, and manage their own servers. Phishing-as-a-Service (PhaaS) has cha...
Featured





