What is Conti ransomware, and how does it work?
Few ransomware operations have achieved the notoriety and scale of Conti. Between 2020 and early 2022, the group reportedly earned hundreds of millions of dollars while attacking hospitals, government agencies, schools, and businesses worldwide. It combined sophisticated technical capabilities with aggressive double extortion tactics, encrypting victims’ data and exfiltrating sensitive information to increase the pressure to pay.
While law enforcement disruption and internal leaks have reduced the Conti group’s activity, its influence persists, and the tactics it used have become popular with other ransomware operations.
In this guide, we'll examine how Conti ransomware operated, explore the most damaging attacks, and outline practical strategies to protect yourself and your organization from similar threats.
What is Conti ransomware?
Conti ransomware is the malware used by the Conti group. The ransomware strain was first widely observed in 2020, with activity increasing significantly from May 2020 onward. It quickly became one of the most prolific ransomware variants, targeting hundreds of organizations primarily in North America and Western Europe.
The Conti group operated a Ransomware-as-a-Service (RaaS) model, where core developers created and maintained the malware while "affiliates" deployed it against victims. These affiliates would pay Conti a percentage of any ransoms they collected.
The group set itself up like a criminal version of a legitimate company, with salaried workers, expert employees, a referral program, and a fully-fledged HR department. Reportedly, some employees were unaware of the true nature of the operation, instead being told that they were working for a penetration testing company.
Conti preferred to target high-value organizations, including:
- Healthcare institutions
- Government agencies
- Educational institutions
- Financial services and legal firms
- Manufacturing and retail businesses
Something that made Conti stand out was its willingness to run attacks with potentially fatal consequences. While some ransomware groups avoid hospitals and emergency services, Conti specifically targeted 911 dispatch carriers, emergency medical services, and law enforcement agencies.
How Conti ransomware works
Conti ransomware followed a methodical attack chain designed to maximize damage and pressure victims into paying a large ransom.
Initial access
Conti affiliates used multiple methods to breach target networks. The most common entry point was phishing emails containing malicious attachments or links. In the notorious attack on Ireland's Health Service Executive (HSE), a single employee opened a malicious Excel attachment, which began the attack sequence that ultimately led to deep access and widespread infection.
Initial access brokers were known to use Trojan malware, like malicious loaders or backdoors delivered via phishing, to establish initial access. They were also quick to weaponize new security flaws; the group exploited compromised Remote Desktop Protocol (RDP) services and leveraged critical flaws like the Log4j vulnerabilities to gain initial access.
Lateral movement
Once inside a network, Conti operators worked to expand their access before deploying the ransomware payload. This reconnaissance phase involved:
- Network mapping: Attackers conducted reconnaissance to understand the network structure and identify high-value systems.
- Credential theft: The group harvested passwords and authentication tokens to escalate privileges and access additional systems.
- Cobalt Strike deployment: Conti heavily relied on Cobalt Strike, a legitimate penetration testing tool repurposed for malicious use. The tool enabled them to maintain access and laterally move within compromised networks.
- Server Message Block (SMB) exploitation: Conti spread across networks using SMB, a protocol designed for file sharing between networked computers, to extend its reach within the network.
The goal was to compromise as many systems as possible before encryption began, maximizing the attack's impact and the pressure on victims to pay.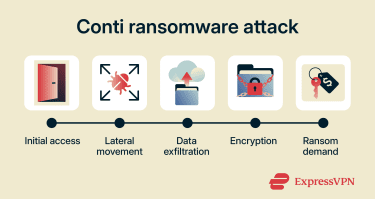
Exfiltration and encryption
Conti ransomware used a combination of 256-bit Advanced Encryption Standard (AES-256) and Rivest–Shamir–Adleman (RSA-4096) encryption, making decryption without the correct key virtually impossible. It also leveraged multi-threaded encryption for rapid file locking, making it significantly faster than most ransomware variants. This speed meant victims had little time to react once encryption started.
As Conti spread through a network, it encrypted files and changed their extensions, rendering them inaccessible. Once encryption was complete, victims would discover ransom notes with instructions for contacting the attackers.
As well as encrypting files, Conti operators would exfiltrate sensitive data and copy it to external servers under their control. This stolen data became leverage for the extortion phase that followed. The exfiltrated data often included sensitive financial, personal, or operational records, which increased the pressure on organizations to pay.
Ransom extortion mechanisms
Conti was one of the first groups to use the double extortion technique, a strategy that has since become standard practice among ransomware groups. The scheme works in two stages:
- Encryption: Attackers lock victims' files and demand payment for the decryption key.
- Exfiltration and data leak threats: If victims refuse to pay, attackers threaten to publish the stolen data on dedicated leak sites.
This approach (sometimes called "pay-now-or-get-breached") puts organizations in an extremely difficult position. Even if they have backups to restore encrypted files, they face potential exposure of sensitive customer data, trade secrets, or confidential communications.
Conti maintained public-facing leak sites where the group published data from non-paying victims, adding reputational damage to the operational disruption. The group was also known to sell access to victim organizations that refused to pay, essentially handing compromised networks to other criminals.
Ransom demands varied based on the victim's perceived ability to pay. For large organizations, demands reached tens of millions of dollars. The Irish HSE, for instance, faced a reported $20 million demand.
Notable Conti ransomware attacks
Conti's victim list spans hundreds of organizations across multiple sectors. However, some attacks stood out for their scale, impact, and the lessons they offered about the group's tactics. Here are three prominent examples.
Tulsa City system shutdown
In May 2021, the city of Tulsa, Oklahoma, was hit by a ransomware attack widely attributed to the Conti group. City IT staff detected that multiple servers were actively communicating with a known threat site, and a ransomware attack had been initiated across several systems.
The city took decisive action, refusing to pay any ransom and instead shutting down all systems to contain the spread. This protective measure came with high costs:
- Online bill payment systems went offline.
- Utility billing was disrupted.
- Email services became unavailable.
- Websites for the City of Tulsa, Tulsa City Council, Tulsa Police, and Tulsa 311 went down for maintenance.
Weeks later, Conti began leaking stolen data. The city warned residents that more than 18,000 files had been published to the dark web, including police citations containing personal information. Exposed data included driver's license numbers, dates of birth, home addresses, and names, putting residents at risk of identity theft and fraud.
City officials advised potentially affected residents to monitor their accounts and credit reports, change their passwords, and enable multi-factor authentication (MFA) on personal accounts.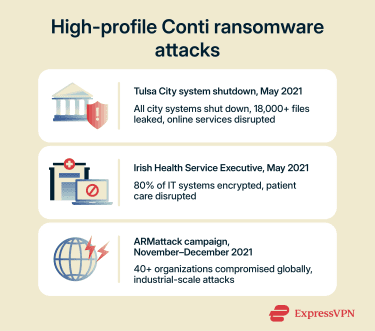
Irish Health Service Executive
The attack on Ireland's HSE in May 2021 was one of the largest known cyberattacks against a health service computer system.
The breach began when a staff member opened a malicious Excel file, allowing attackers to establish a foothold in the network. From there, Conti was able to move through HSE and Department of Health systems, eventually deploying the ransomware.
The impact was severe:
- All HSE IT systems nationwide were shut down.
- The HSE was forced to cancel appointments, including many for pregnant women at Dublin's Rotunda Hospital.
- 80% of the HSE IT environment was encrypted, and patient care was severely disrupted across the entire Irish healthcare system.
- The attack occurred during the COVID-19 pandemic, compounding the crisis and exposing the private information of thousands of people who had received the COVID-19 vaccine.
Conti demanded 20 million dollars not to release exfiltrated data. In an unusual twist, the attackers eventually provided the decryption key for free, though they continued threatening to leak stolen data.
The HSE stated publicly that no ransom was paid. Recovery, however, took months and reportedly cost the Irish government tens of millions of euros. The incident prompted significant investment in healthcare cybersecurity across Ireland and became a case study in critical infrastructure vulnerability.
ARMattack campaign
In late 2021, Conti demonstrated its operational capacity with a campaign that security researchers codenamed ARMattack. Running from November to December 2021, the campaign compromised more than 40 organizations worldwide. This represented an average of more than one successful attack per day, showcasing the scale and efficiency of Conti's affiliate network.
Key characteristics of the ARMattack campaign:
- Geographic focus: U.S.-based companies were most heavily targeted, with additional victims in Europe, the United Arab Emirates, and India.
- Industry targets: Manufacturing, real estate, logistics, professional services, and trade were the most affected sectors.
- Speed: In the fastest successful attack, operators moved from initial access to full system encryption in just three days.
The ARMattack campaign demonstrated that Conti had evolved into a highly organized criminal enterprise capable of conducting industrial-scale cyberattacks.
Is Conti ransomware still active?
Conti, as a group, no longer operates, but its influence persists in today's threat landscape, and its members are still active in other threat groups.
The group's decline began in February 2022 when an individual leaked approximately 60,000 internal chat messages from Conti's operations, exposing their tactics, internal structure, and even conflicts between members.
Despite the leaks, Conti continued attacking targets (including Costa Rican government systems) into May 2022. However, later that month, researchers tracking the group’s online infrastructure said key internal systems appeared to have been taken offline.
While the Conti brand officially shut down, security researchers reported that many of its former members moved on to other ransomware operations, including groups such as Black Basta and Akira. Leaked Conti code has also been incorporated into newer ransomware variants, demonstrating that the group’s technical innovations continue to influence the threat landscape.
How to prevent Conti ransomware attacks
Defending against Conti-style ransomware requires a layered security approach combining technical controls, human awareness, and a detailed recovery plan.
Technical controls
Implementing strong technical defenses can help to address the vulnerabilities Conti exploited most frequently. This includes:
- MFA: Organizations should require MFA for all remote access, administrative accounts, and email systems. This prevents attackers from using stolen credentials to access networks.
- Patch management: Conti routinely exploited known vulnerabilities; maintain a comprehensive patching schedule, prioritizing internet-facing systems and critical infrastructure.
- Network segmentation: Divide networks into isolated segments (or subnets) to limit lateral movement. If attackers compromise one area, segmentation prevents them from reaching critical systems.
- Endpoint detection and response (EDR): Deploy modern security tools capable of detecting behavioral anomalies, not just known malware signatures. Conti's obfuscation techniques were designed to evade traditional antivirus software.
- Disable unnecessary services: Secure or disable RDP and SMB services where not required. These protocols were primary lateral movement vectors.
- Email security: Implement filtering to help block phishing emails before they reach users. Consider solutions that sandbox attachments and scan links.
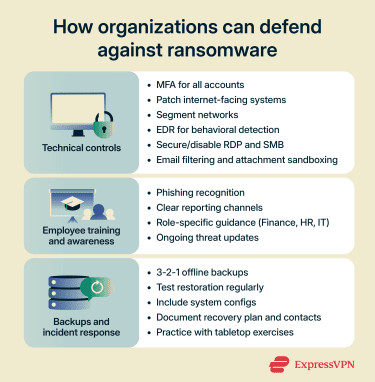
Employee training and awareness
Technical controls mean little if users invite attackers inside. Effective security awareness programs for staff should include:
- Phishing recognition training: Teach employees to identify suspicious emails and social engineering tactics. Regular simulated phishing exercises reinforce these lessons.
- Reporting culture: Create clear channels for reporting suspicious activity without fear of blame or false alarms. Early reporting can stop attacks before they spread.
- Role-specific training: Provide additional guidance for high-risk roles like finance, HR, and IT administrators who are frequently targeted.
- Regular updates: Share information about current threats and attack methods. New tactics are developed all the time, which means training has to be ongoing.
Backups and incident response
When prevention fails, preparation helps minimize the damage from Conti-style ransomware attacks.
Backup strategy
Organizations should maintain offline backups that cannot be accessed by attackers who have compromised the primary network. Following the widely recommended 3-2-1 rule helps reduce risk: keep three copies of data, store them on two different types of media, and ensure at least one copy is kept offsite or offline.
Regularly testing restoration processes is equally important, as backups only provide value if they can be successfully recovered during an emergency. It’s also critical to back up not just data files but system configurations as well, so operations can be restored more quickly and completely.
Incident response planning
Companies need a documented incident response plan tailored specifically to ransomware scenarios. That plan should clearly identify key external contacts, including legal counsel, cyber insurance providers, digital forensics specialists, and relevant law enforcement agencies.
Clear communication protocols must be established in advance to guide how and when affected parties will be notified. Finally, organizations should regularly rehearse their response procedures through tabletop exercises, ensuring that teams understand their roles and can act quickly under pressure.
FAQ: Common questions about Conti ransomware
How does Conti ransomware spread?
What makes Conti ransomware different?
How can organizations defend themselves against ransomware?
- Technical controls: Multi-factor authentication (MFA), aggressive patching, network segmentation, and modern endpoint detection tools.
- Employee training: Regular phishing awareness programs and clear reporting procedures.
- Backup strategy: Tested, offline backups following the 3-2-1 principle.
- Incident response planning: Documenting procedures and practicing them before an attack occurs.
No single measure provides complete protection; effective defense requires all these elements working together.
What should victims do after infection?
Take the first step to protect yourself online. Try ExpressVPN risk-free.
Get ExpressVPN