Expressvpn Glossary
Unauthorized acces

What is unauthorized access?
Unauthorized access is the act of obtaining access to a network, system, application, or device without permission or authorization. It typically involves bypassing authentication or authorization controls, often through stolen, guessed, or misused credentials.
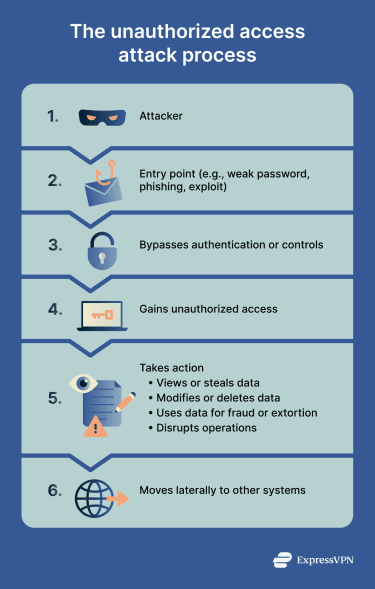
How does unauthorized access work?
Unauthorized access usually works by bypassing or defeating security controls on a system or network. Once inside the system, attackers may be able to view, copy, modify, or delete sensitive data and disrupt operations.
Unauthorized access can occur by several means:
- Weak or stolen passwords: Easy-to-guess credentials or brute-force attacks.
- Compromised accounts: Misused credentials granting access to connected systems or data.
- Social engineering: Phishing or impersonation to trick users into revealing login details.
- Exploited software vulnerabilities: Including zero-day exploits and unpatched security flaws.
- Malware: Trojans, worms, or other malicious software that steal data or maintain access.
Why is unauthorized access important to prevent?
Unauthorized access is critical to prevent because it can expose sensitive data, leading to data theft or account takeover. It can enable fraud, ransomware attacks, and extortion, while also potentially disrupting operations and availability.
Once attackers gain access, they often move laterally across networks, compromising additional systems. For organizations, these breaches may trigger compliance violations and legal penalties, as well as reputational damage.
Where does it happen?
Unauthorized access can happen in any environment that secures data or systems behind access controls. This can include personal accounts (like email or social media), company networks, financial systems (such as banking apps), software databases, cloud platforms, APIs, administrative dashboards, and connected devices such as home routers or Internet of Things (IoT) systems.
Risks and privacy concerns
If someone gains unauthorized access to a system, they may:
- Access, copy, or delete sensitive data.
- Misuse the system to launch further attacks.
- Carry out fraud by stealing money or goods.
- Disrupt services or operations.
- Monitor and leak private communications or browsing activity.
- Maintain persistent access via backdoors.
Understanding how unauthorized access happens helps individuals and organizations reduce their risk and strengthen their security.
Further reading
- Data theft: What it is and how to protect yourself
- Brute force attack: What it is and how to prevent it
- Rainbow table attack: What is it and how to stay safe
- Email address found on the dark web? Here’s what to do
- What is two-factor authentication (2FA), and how to set it up securely
- The ultimate guide to phishing detection
- Phishing-as-a-Service (PhaaS): What it is and why it’s dangerous


